Goverment HLS

Government Homeland Security Solutions
- Extensive HLS domain expertise
- End-to-end service delivery
- Integrated solutions and consulting
- Dedicated training and knowledge transfer
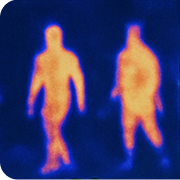
Border protection
Territorial Awareness. Coordinated Response.
Our expertise extends to the design and deployment of comprehensive, multi-layered border surveillance and protection systems – each tailored to meet the unique operational, geographical, and security requirements of our clients. Our holistic border security approach integrates four core pillars:
Dignitary Protection
Protecting Leadership. Ensuring Continuity.
Our expert security team delivers comprehensive know-how, advanced technologies, and professional training to ensure the highest level of protection for high-profile individuals. From personalized training programs to full-scale team development, we equip protective details with the skills and capabilities needed for every scenario. Our services also include tailored solutions for secure convoy operations and safe, efficient VIP transfers – all designed to minimize risk and maintain seamless continuity of movement.
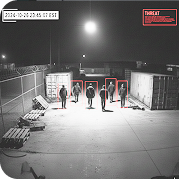
Site Protection
Securing Critical Assets. Enabling Resilience.
As highlighted on our Enterprise HLS Solutions page (link), Mer specializes in delivering comprehensive security solutions for critical sites and infrastructure. Our approach is built on a
proven methodology of in-depth risk assessment, ensuring that every protective and response measure is precisely aligned with each site’s unique threat profile. We design and tailor security architectures according to governmental priorities and operational needs, creating robust, scalable solutions that safeguard essential assets and ensure long-term resilience.
Counterterrorism
Anticipating Threats. Strengthening Preparedness.
Our team of experts – all former senior officials from Israel’s security community – bring decades of operational experience in counterterrorism, national security, and strategic planning. Drawing from this deep expertise, we have developed proven doctrines, methodologies, and best practices that can be fully adapted and customized to the unique challenges and operational realities of any country. Our counterterrorism specialists work closely with you to define your operational environment, identify relevant threat typologies, and select the most effective technological and tactical solutions to meet your specific needs. The result is a tailored, resilient security framework designed to enhance national preparedness and response capabilities.
Internal threats
Protecting Leadership. Ensuring Continuity.
In today’s digital landscape, social media, messaging applications and dark-web platforms have increasingly become hubs for illicit activity and covert communication. Leveraging our extensive expertise in intelligence and cyber domains, we deliver the doctrines, tools, and operational frameworks needed to effectively detect, monitor, and mitigate these emerging threats.
Our tailored solutions empower you to navigate this sensitive environment with confidence, ensuring proactive risk identification, rapid response, and enhanced national security.

Let’s Strengthen National Security